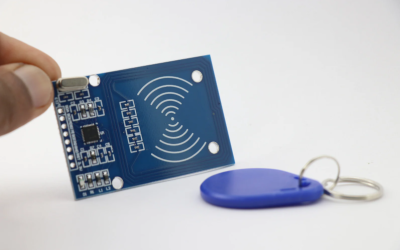
Have you ever considered how secure your office or hotel key cards really are? Recent research by French security firm Quarkslab has uncovered a serious vulnerability that could impact millions of contactless cards worldwide. These cards, produced by Shanghai Fudan...
Welcome to Cyber Safe Resources
Welcome! You’ll find simple, practical resources to help you build safer online habits. We update articles regularly. Be part of our community—subscribe to the newsletter to stay informed and empowered.
The Impact of GDPR on Small Businesses
Since its implementation in May 2018, the General Data Protection Regulation (GDPR) has had a significant impact on businesses around the globe, including small businesses. Understanding GDPR is crucial for any business that processes the data of European Union (EU)...
How Regular Software Updates Protect Your Business
Have you ever delayed a software update? It’s a common scenario in both personal and professional settings, but regularly updating your software is one of the simplest, yet most effective ways to protect your business from cyber threats. Here’s why keeping your...
Understanding the Risks of BYOD (Bring Your Own Device)
As small businesses embrace the flexibility and cost savings of Bring Your Own Device (BYOD) policies, understanding the associated risks is crucial. While BYOD can increase productivity and employee satisfaction, it also introduces several cybersecurity challenges....
The Basics of Secure Password Management
Are you confident that the passwords protecting your business's critical data are secure enough? Passwords are the first line of defence against unauthorized access to your systems and managing them securely is essential. Here’s a guide to the basics of secure...
How to Foster a Culture of Cybersecurity Awareness in Your Business
Is your business's cybersecurity as strong as it could be? The answer often lies not just in the technology you use but in the culture of awareness you foster within your organization. Creating a culture of cybersecurity awareness is essential for ensuring that all...
Stay Ahead: Emerging Cybersecurity Trends for Small Businesses
As technology evolves, so does the landscape of cybersecurity threats. Staying ahead of these trends is crucial for small businesses aiming to protect their digital assets and maintain trust with customers. Here’s a look at some of the emerging cybersecurity trends...
Why Should Your Small Business Implement Multi-Factor Authentication?
Is your small business's cybersecurity relying solely on passwords? If so, it might be time to consider an upgrade. Multi-Factor Authentication (MFA) is a security must-have that adds an essential layer of protection, making it significantly harder for cybercriminals...
Is Your Business Ready to Handle a Cybersecurity Incident?
How prepared is your small business to handle a cybersecurity incident today? With cyber threats becoming increasingly sophisticated, having a solid incident response plan is more critical than ever. Such a plan not only helps mitigate the damage of potential attacks...
Why is Secure Web Browsing Essential for Your Small Business?
Have you ever considered how your web browsing habits can impact the security of your small business? Secure web browsing is more than just a precaution; it's a necessary part of protecting your business's online activities from cyber threats.Every time your employees...
Choosing Cybersecurity Tools: A Practical Guide for Small Businesses and Everyday Users
electing security tools can feel overwhelming. The goal isn’t to buy “everything”—it’s to match the right protections to your real risks, implement them well, and keep them maintained.1) Start with a quick risk snapshotWhat do you need to protect? (customer data,...
Why Should Regular Cybersecurity Audits Be Non-negotiable?
In today’s fast-moving digital environment, cybersecurity audits aren’t a “nice to have”—they’re essential. Audits help small businesses understand where they’re strong, where they’re exposed, and what to fix first.Why Audits MatterRegular audits:Find vulnerabilities...